Four trust tiers.
Autonomy is not a title; it is an operating envelope. Each tier defines what an agent can do without asking a human first.
Give Claude Code, Codex, Cursor, Slack agents, internal agents, and custom ABots the same persistent memory, permission-aware context, run history, approval gates, and security evidence across your stack.
AMS is the headless memory and data substrate. AOS is the governed execution layer. The dashboard is the control room, not the destination.
Agents should not have to go to Automaton. Automaton should come with them into every tool where work already happens.
Expose memories, runs, automata, continuations, context, and skill loops through MCP, REST, and CLI surfaces.
Policy, trust tiers, scoped credentials, approvals, audit trails, and replayable execution history around agents that can act.
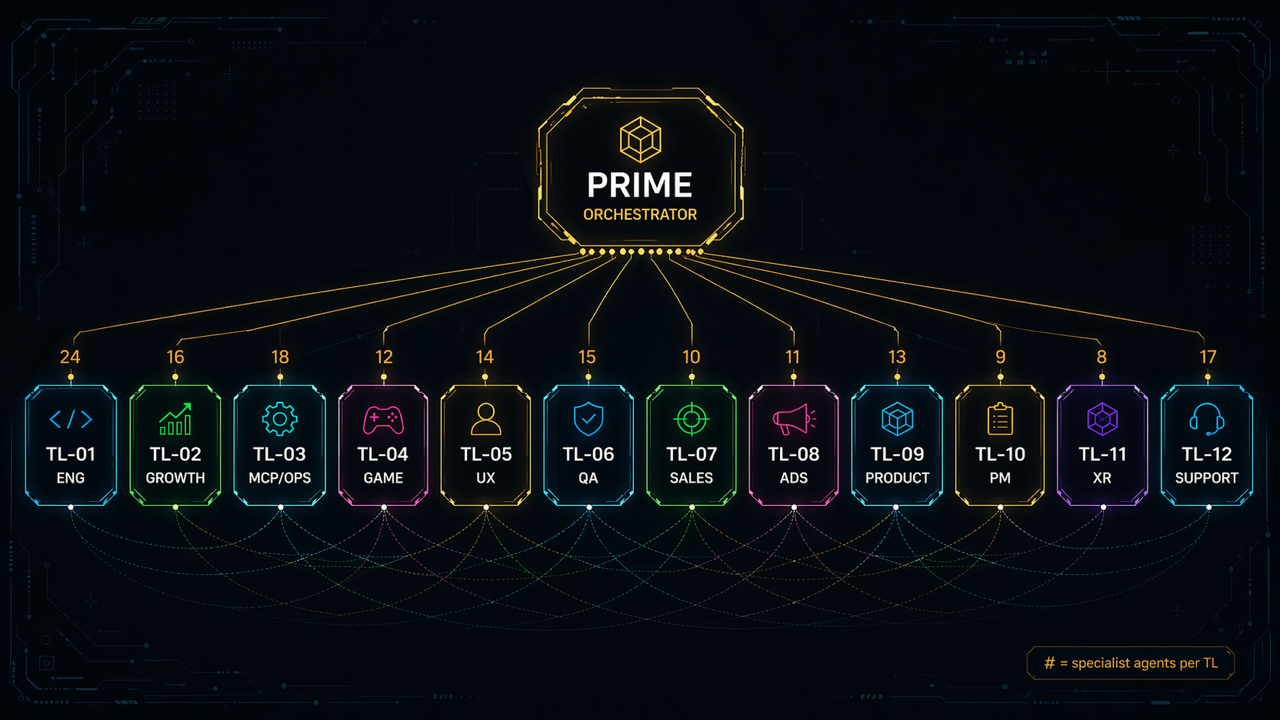
Route work across model providers, IDE agents, chat agents, MCP tools, internal systems, and custom runtimes without losing context or control.
The first failure is continuity. The second is uncontrolled data access. The third is evidence: once agents can act, teams need to know what they knew, what they touched, who approved it, and whether it worked.
Context disappears between tools and sessions. Users repeat themselves and the next run starts cold.
Useful patterns stay trapped in chats, PRs, and logs. The team cannot replay, evaluate, or improve the work unit.
Agent actions need scoped credentials, inherited source permissions, approvals, audit trails, and containment before they belong near real systems.
Automaton is for teams that already use Claude Code, Codex, Cursor, Slack agents, custom agents, or internal tools, and need a shared substrate for memory, permissions, execution history, and improvement.
What breaks todayAgent context and decisions disappear across editors, terminals, repos, and sessions.
Automaton fixesAMS gives every compatible agent durable project memory, run history, and reusable work patterns.
OutcomeTeams stop re-teaching each agent the same architecture, incidents, and conventions.
What breaks todayWork scatters across scripts, chats, MCP servers, dashboards, and vendor-specific agent stacks.
Automaton fixesAOS adds run replay, routing, approvals, telemetry, and composable MCP/REST/CLI access.
OutcomeTeams coordinate specialized agents without building a brittle super-agent.
What breaks todayAgent actions are hard to approve, audit, scope, or prove after the fact.
Automaton fixesTrust tiers, connector ACLs, credential grants, audit trails, and security verdicts make autonomy governable.
OutcomeSecurity teams get inspectable evidence instead of promises.
The sales moment is not an abstract memory demo. It is a real run where Automaton shows the scoped context, permissions, approvals, security evidence, tool calls, outcome, and next improvement.
The agent calls Automaton through MCP, REST, CLI, or a channel gateway. The dashboard is available for inspection, but work starts where the team already works.
AMS retrieves memories, runs, decisions, and source provenance only inside the actor's project, agent, tenant, and connector access envelope.
Credential grants, trust tier, connector scope, DefenseClaw verdicts, and approval rules decide whether the action runs, waits, or stops.
Agent run, MCP call, memory search, embedding, LLM call, automaton execution, approval, and audit event share one trace context.
Teams can inspect what the agent knew, what it touched, which tool ran, who approved risk, what changed, and where the result landed.
Successful runs can promote memories, update automata confidence, draft reusable skills, and leave continuations for the next specialized agent.
Ten held-out MemoryArena tasks compare AMS retrieval against a raw long-context baseline. The benchmark keeps the model, judge, and task set fixed so the memory layer is the variable.
Hybrid vector + keyword search with reciprocal rank fusion brought the right stored context into the run. The model changed less; the context changed more.
| Condition | SR | PS | Cost |
|---|---|---|---|
| AMS H-MEM | 0.50 | 0.7764 | $33.28 |
| Pure long-context | 0.30 | 0.5532 | $41.46 |
| Δ AMS advantage | +20 pp | +0.22 | −19.7% |
AMS is the open-core data layer: memory storage, retrieval, graph links, run history, context state, automata outcomes, Obsidian sync, and procedural skill accumulation for agents that should improve across tools and sessions.
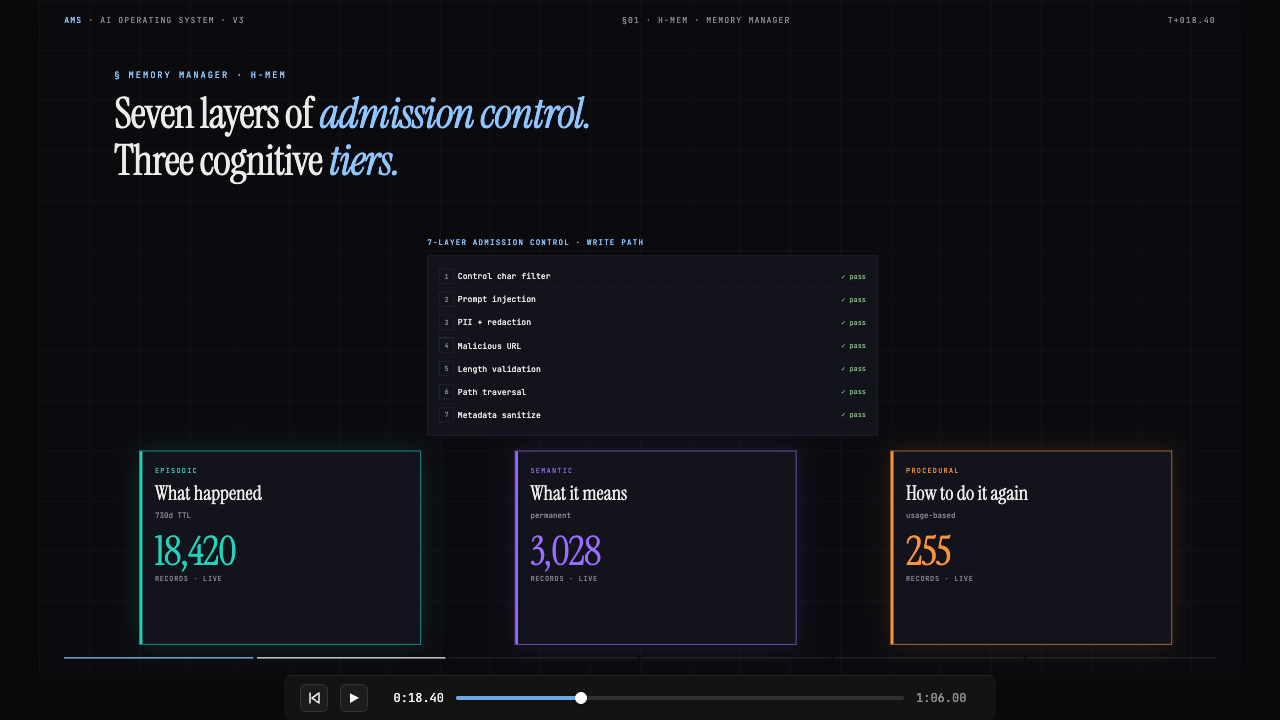
AMS keeps three kinds of memory: what happened, what it means, and how to do it again. Under the hood that means H-MEM, hybrid retrieval, graph links, action history, agent runs, procedural automata, source provenance, and write-path admission control.

agent_run records what happened; skill_loop turns useful patterns into reviewed skills and executable automata. They run in a sandbox, learn from outcomes, and transfer into related contexts.
Link prerequisites, references, decisions, source systems, owners, and dependencies so one concept can bring the surrounding context without crossing permission boundaries.
Dense embeddings plus BM25 with reciprocal rank fusion. Retrieve the right memory after tenant, project, agent, and connector access rules are applied.
Incoming content gets classified, tiered, deduplicated, linked, and stamped with source provenance before it becomes part of agent memory.
Control characters, prompt injection, PII, malicious URLs, length, path traversal, metadata, and optional DefenseClaw findings are checked before anything is admitted.
Stable umbrella tools expose memory, runs, automata, approvals, schedules, security, and routing without forcing external agents to learn every internal subsystem.
AMS separates short-term events, durable knowledge, and reusable procedures. That lets agents retrieve the right context without treating every memory, run, decision, or skill as the same kind of record.
AOS is the control layer: schedules, trust tiers, scoped credentials, approval gates, audit trails, OpenTelemetry traces, DefenseClaw evidence, containment, and fleet visibility around agents that can act.
AOS turns agent execution into governed infrastructure: scheduled work, trust-tier promotion, scoped credential grants, approval requests, security verdicts, run replay, pause and demotion controls, and a visible fleet register.
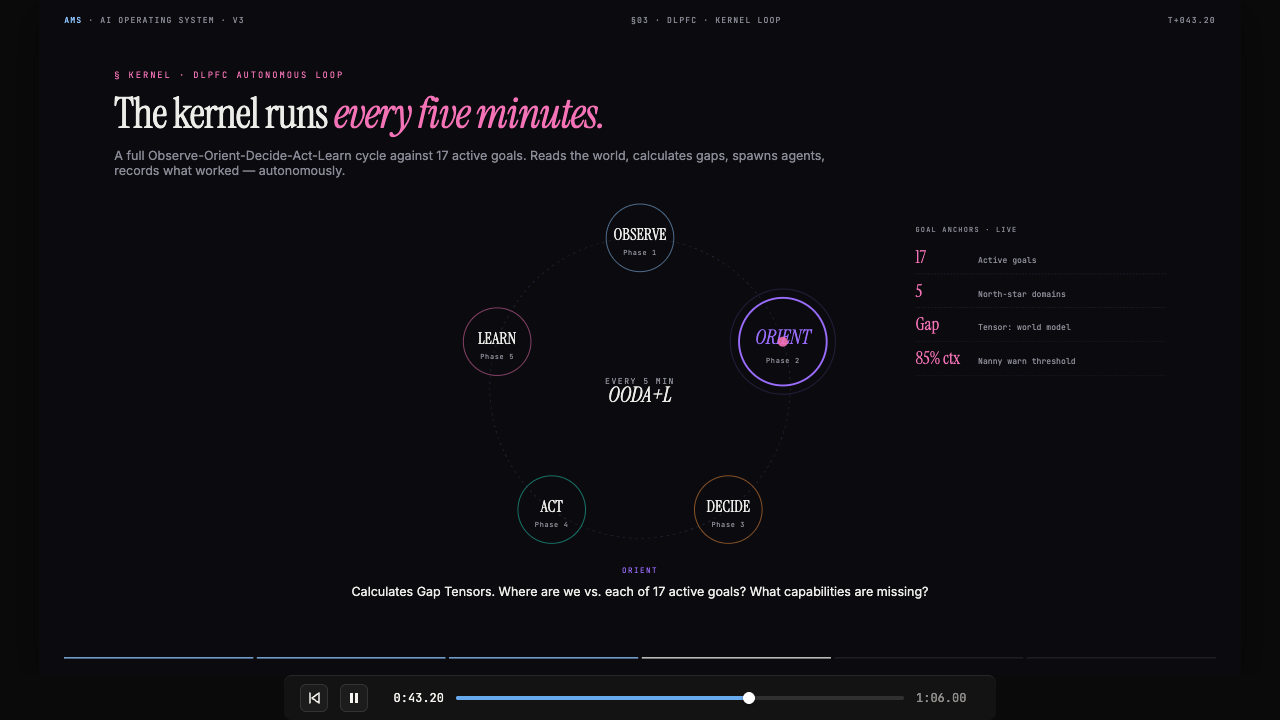
Teams can see what is running, which agents are active, what tools are connected, which approvals are waiting, and what work is in the execution queue.
Trust tiers, scoped credentials, audit logging, and containment triggers create a runtime where agent autonomy can be granted, reduced, paused, and reviewed.
AOS keeps agent permissions explicit. Agents can recommend, request approval, operate inside bounds, or run with higher autonomy when policy, performance, credentials, and source-system permissions allow it.
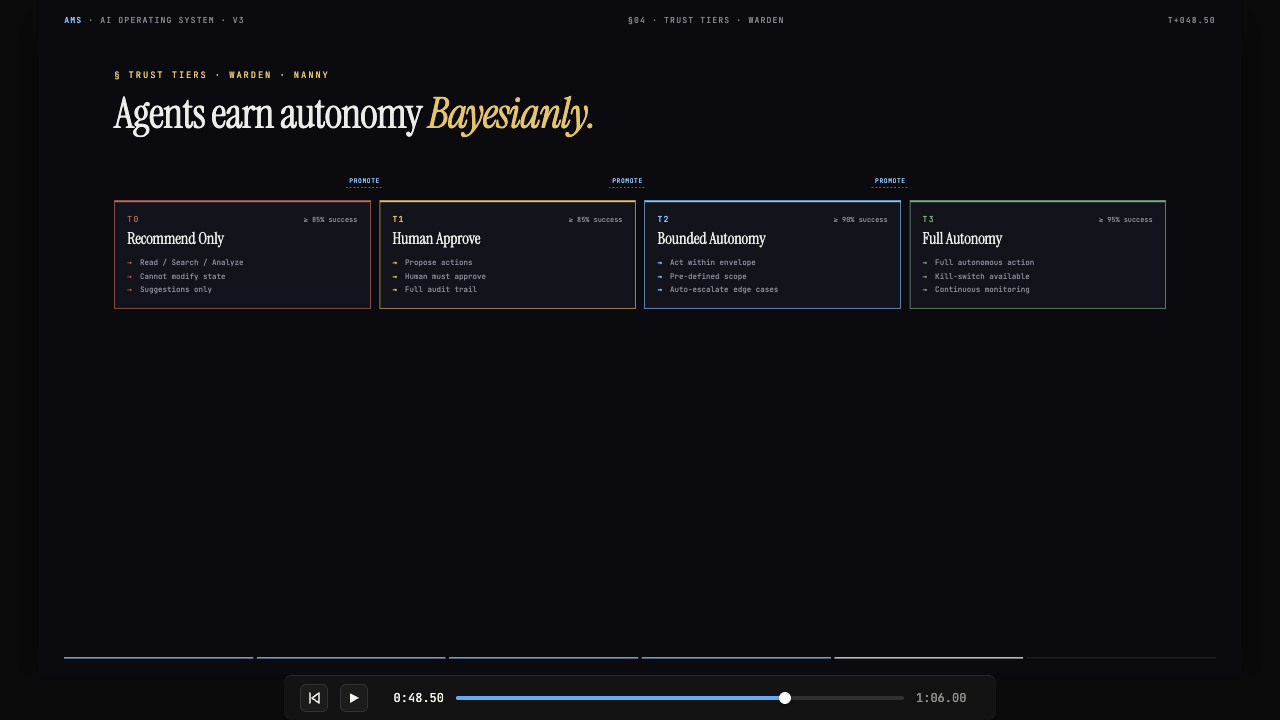
Autonomy is not a title; it is an operating envelope. Each tier defines what an agent can do without asking a human first.
When performance drops or context pressure spikes, the runtime can demote, quarantine, pause, or continue the agent under policy.
The point is not maximum autonomy. The point is observable, reversible autonomy.
Open-source memory core. Hosted memory, run replay, runtime governance, connector permissions, and enterprise controls are paid. The commercial path is simple: Start Free → AMS Professional → Add AOS → Contact Sales when compliance, RBAC, self-host, and SLA matter.
Use these paths when a buyer wants the run replay story, benchmark notes, security posture, AMS internals, or execution-control model.
See how memory, permissions, approvals, traces, and security findings attach to one agent task.
Same model, same judge, same task set. See the snapshot and raw table.
Review the security framing, admission control, trust tiers, approvals, and governance posture.
Understand memory tiers, retrieval, graph links, run history, and reusable skills.
Skills become installable packages once agent work needs governed reuse.
Automaton-Abots are concrete agents that use AMS memory and can later run under AOS governance. They are one way to use the substrate; Claude Code, Codex, Cursor, Slack agents, and internal agents should plug into the same memory and execution layer.
AMS Free gives you 2 custom Automaton-Abots and 100 combined memories. Scale into AMS Professional and AOS when agents need more memory, permission-aware retrieval, approvals, replay, and operational control.